Today's picks
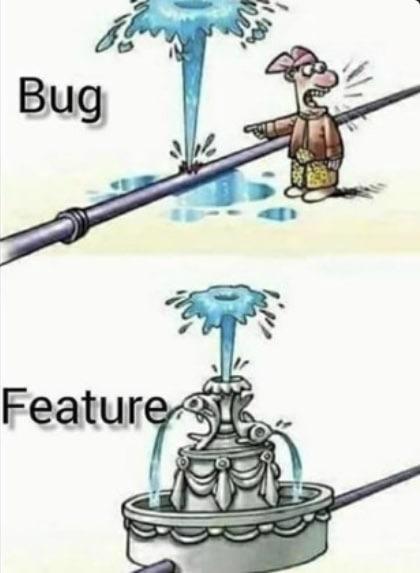
When Bugs Turn Into Features
Programming
10.8M views
22 hours ago

Fenge Dual Monitor Stand, Monitor Riser with Drawer, 42.5 Inch Large Computer Monitor Stand for 2 Monitors, 2 Tier Wooden Desk Shelf for Top of Desk
Affiliate
$89.99

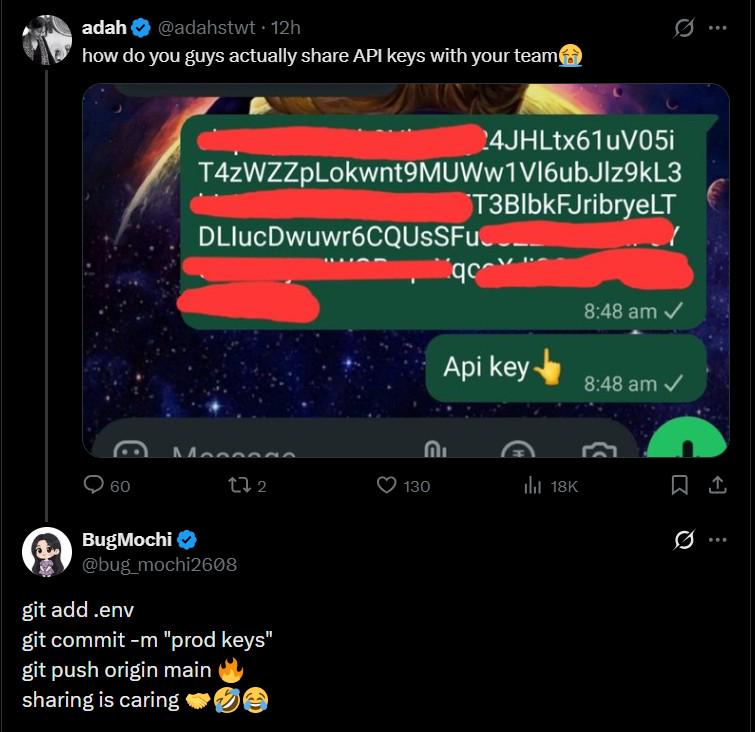
Yeah you can obviously break into CIA servers in 30 seconds
Programming
77.6K views
4 years ago

 AI
AI
 AWS
AWS
 Agile
Agile
 Algorithms
Algorithms
 Android
Android
 Apple
Apple
 Bash
Bash
 C++
C++