HTTP 418: I'm a teapot
The server identifies as a teapot now and is on a tea break, brb
HTTP 418: I'm a teapot
The server identifies as a teapot now and is on a tea break, brb
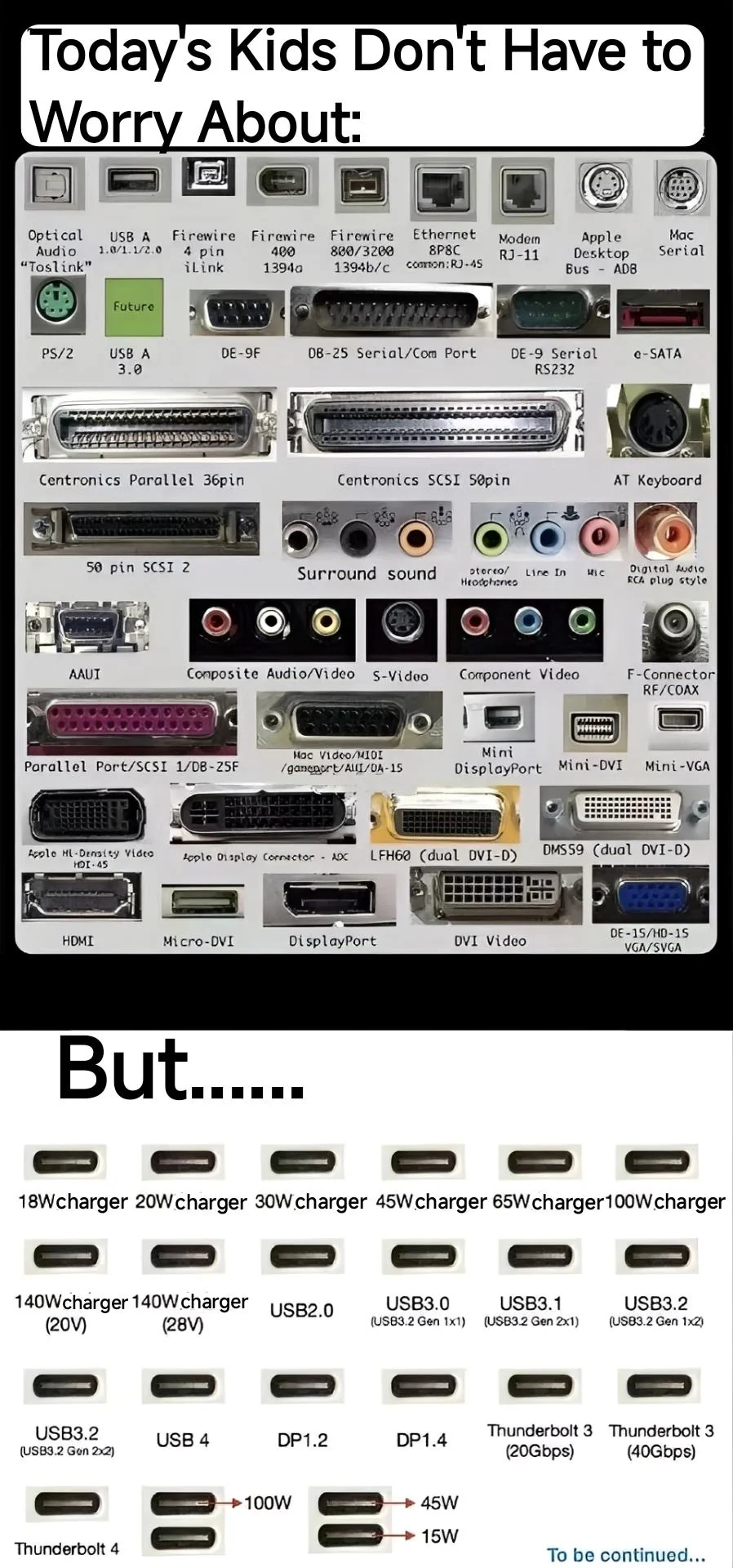
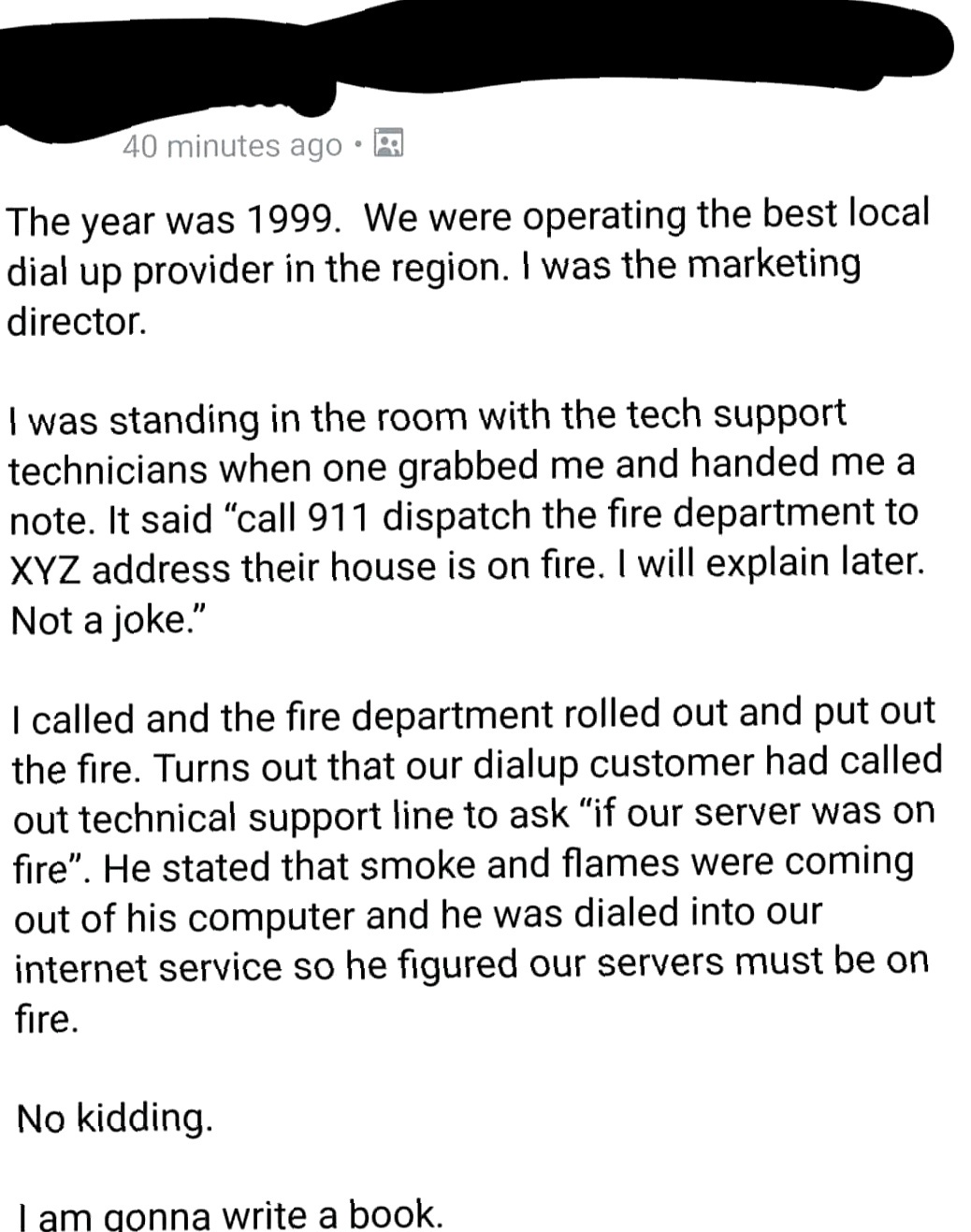
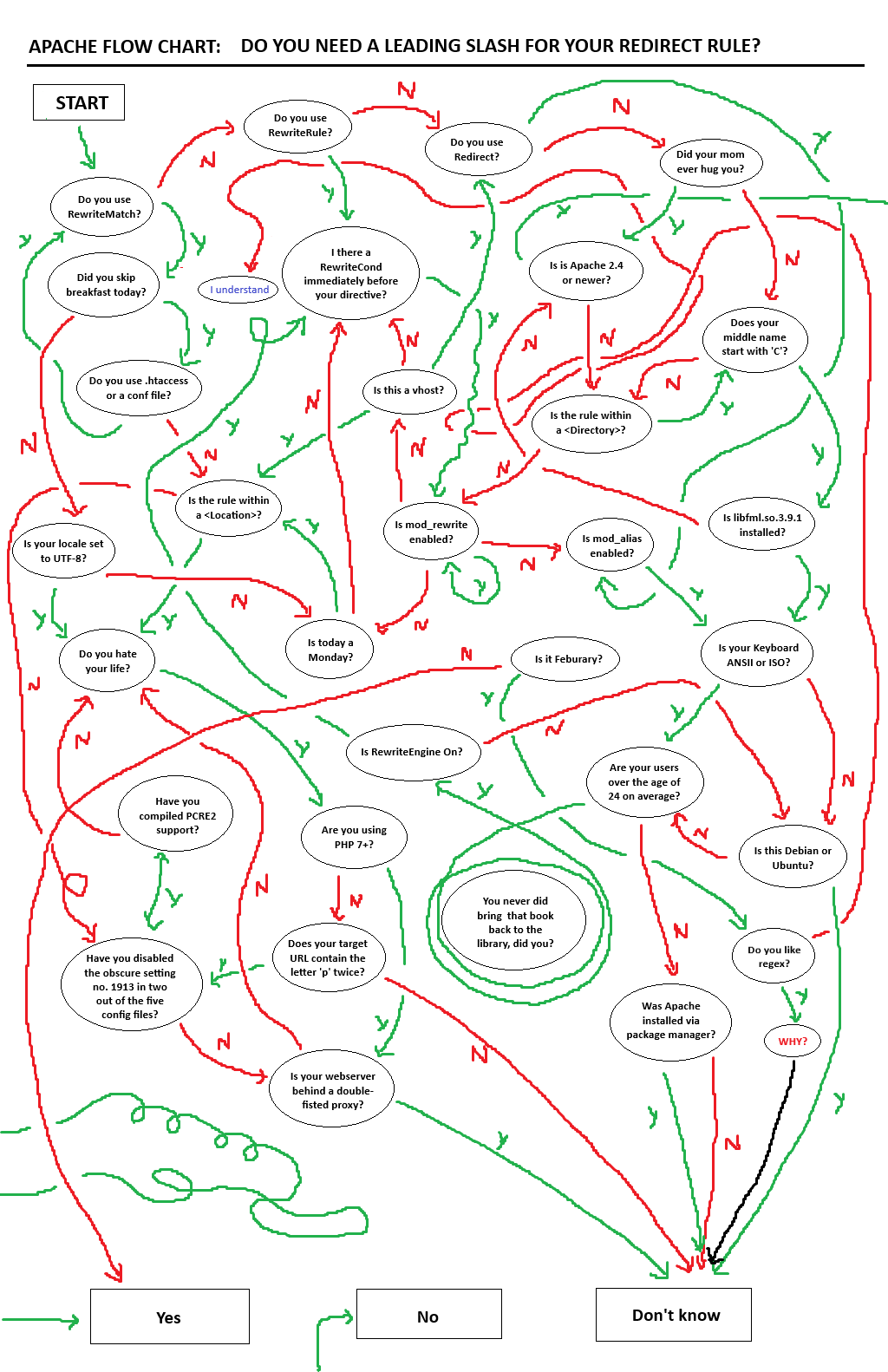
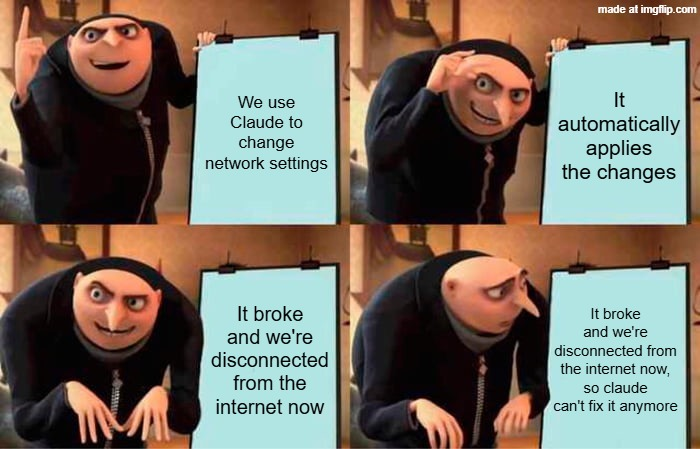
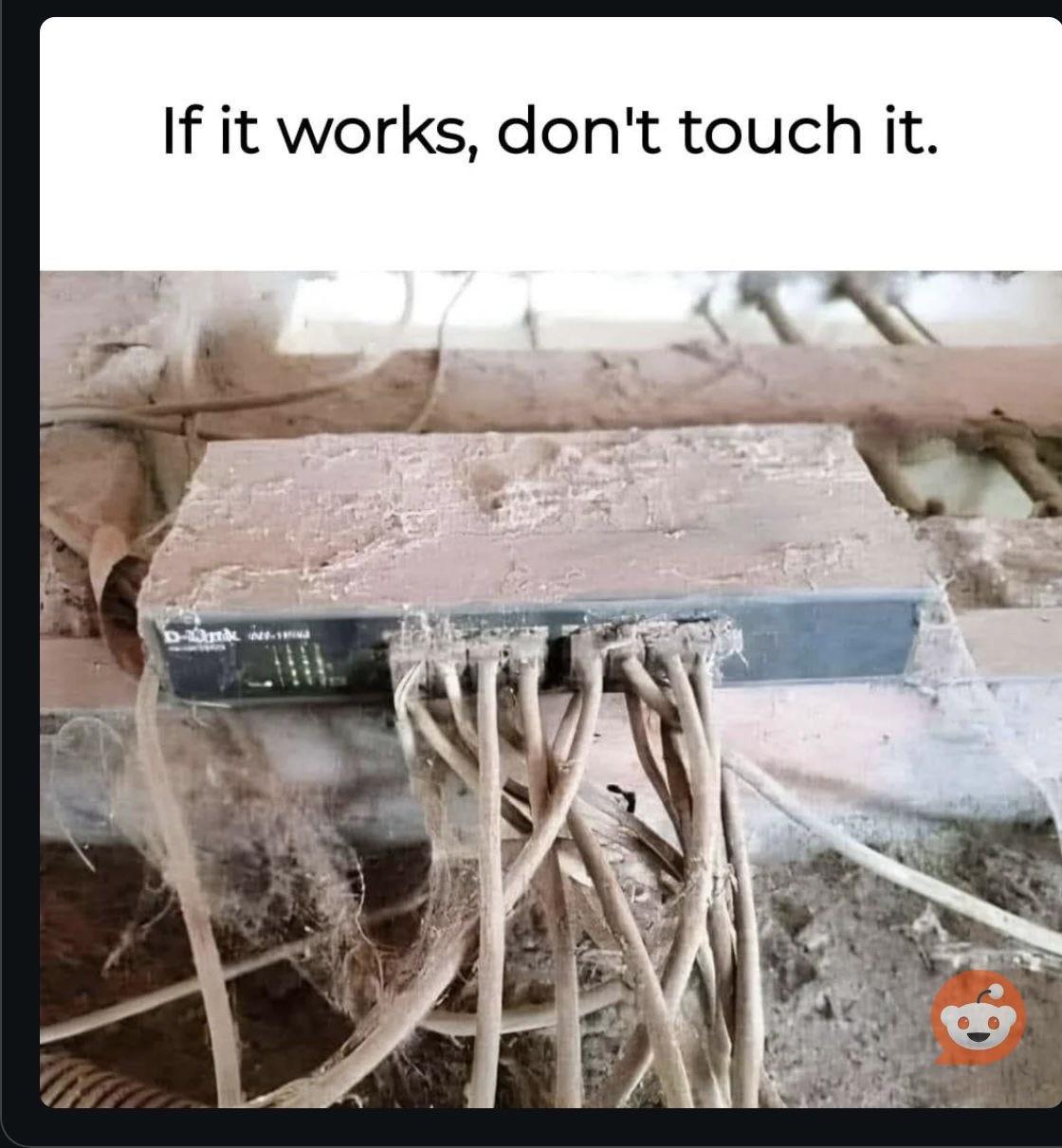
Networking Memes
Networking: where packets go to die and engineers go to question their career choices. These memes are for anyone who's spent hours debugging connection issues only to discover a typo in an IP address, explained BGP to non-technical people, or developed an unhealthy relationship with Wireshark. From the mysteries of DNS propagation to the horror of legacy network configurations held together by virtual duct tape, this collection celebrates the invisible infrastructure that everyone notices only when it stops working.

 AI
AI
 AWS
AWS
 Agile
Agile
 Algorithms
Algorithms
 Android
Android
 Apple
Apple
 Bash
Bash
 C++
C++