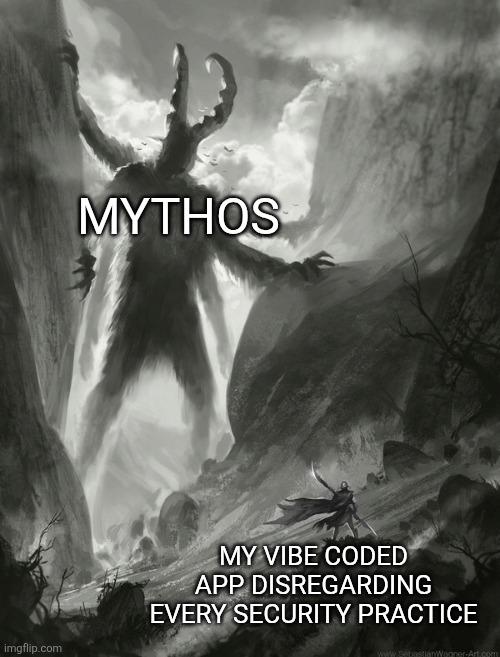
When you skip OAuth, JWT validation, input sanitization, HTTPS, rate limiting, CORS policies, and basically treat security headers like optional dependencies, you've achieved what cryptographers call "security through obscurity" but what we call "security through nonexistence." The logic is flawless: hackers can't find vulnerabilities in security measures that were never implemented in the first place. It's like saying you can't have a memory leak if you never free any memory—technically correct, but also... completely wrong. Your vibe-coded app standing there confidently while Mythos (representing actual security threats) looms overhead is the energy of every developer who's ever shipped to prod with "TODO: add auth later" still in the codebase.
Cannot Exploit If No Security Is Applied
1 month ago
457,079 views
0 shares
security-memes, webdev-memes, backend-memes, bad-practices-memes, vibe-coding-memes | ProgrammerHumor.io
More Like This
Gets Phished By It Anyways
3 months ago
337.0K views
1 shares

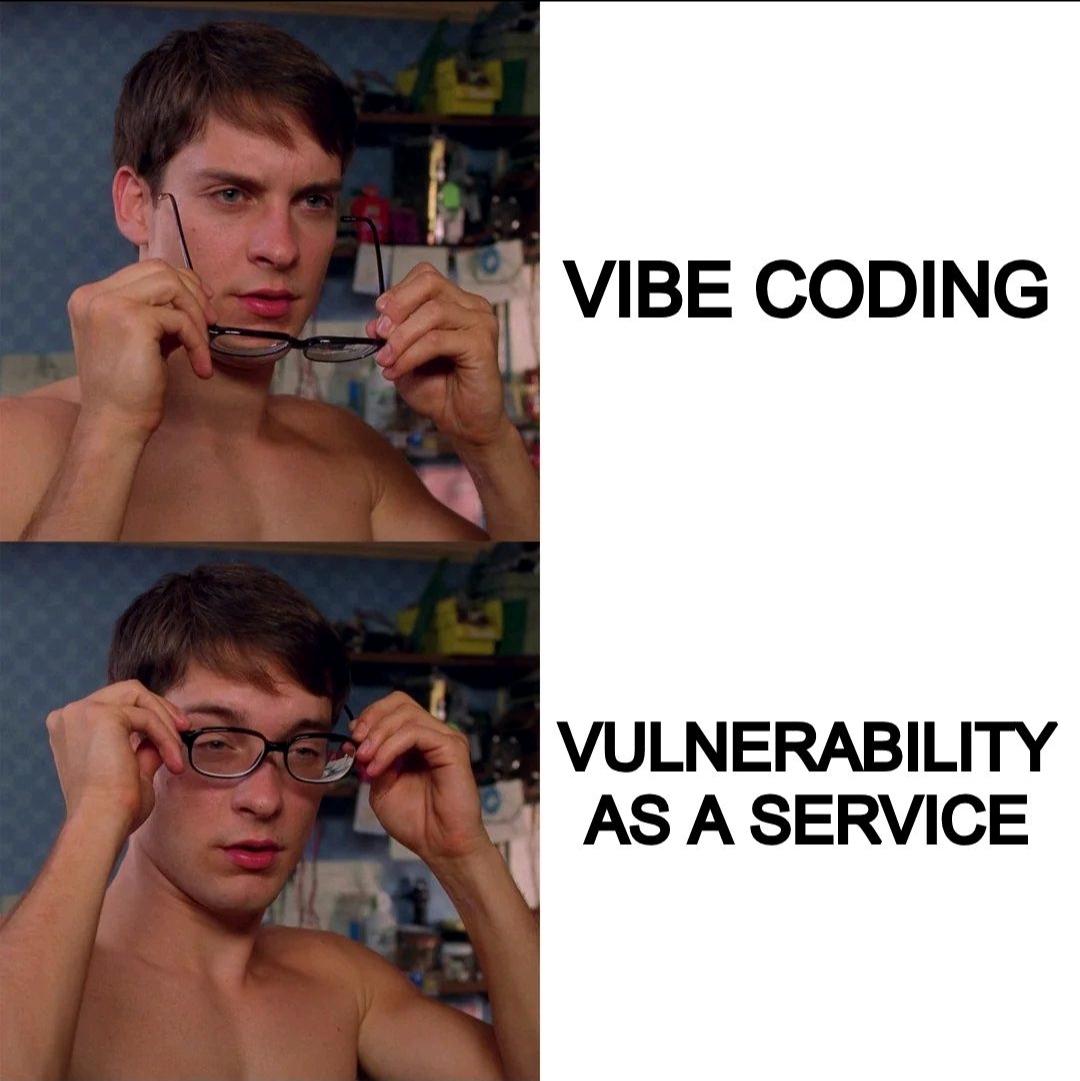
Yes You Can Vibe Code That!
12 months ago
428.0K views
1 shares
The DDoS Attack Is Coming From Inside The House
7 months ago
393.1K views
0 shares

Loading more content...

 AI
AI
 AWS
AWS
 Agile
Agile
 Algorithms
Algorithms
 Android
Android
 Apple
Apple
 Bash
Bash
 C++
C++
 Csharp
Csharp