Today's picks
Weone Artwork 4 Panel Canvas Wall Art binary code motherboard information technology Stretched & Framed Art Prints Modern Painting Wall Decoration Ready to Hang Unique Designed
Affiliate
$59.99
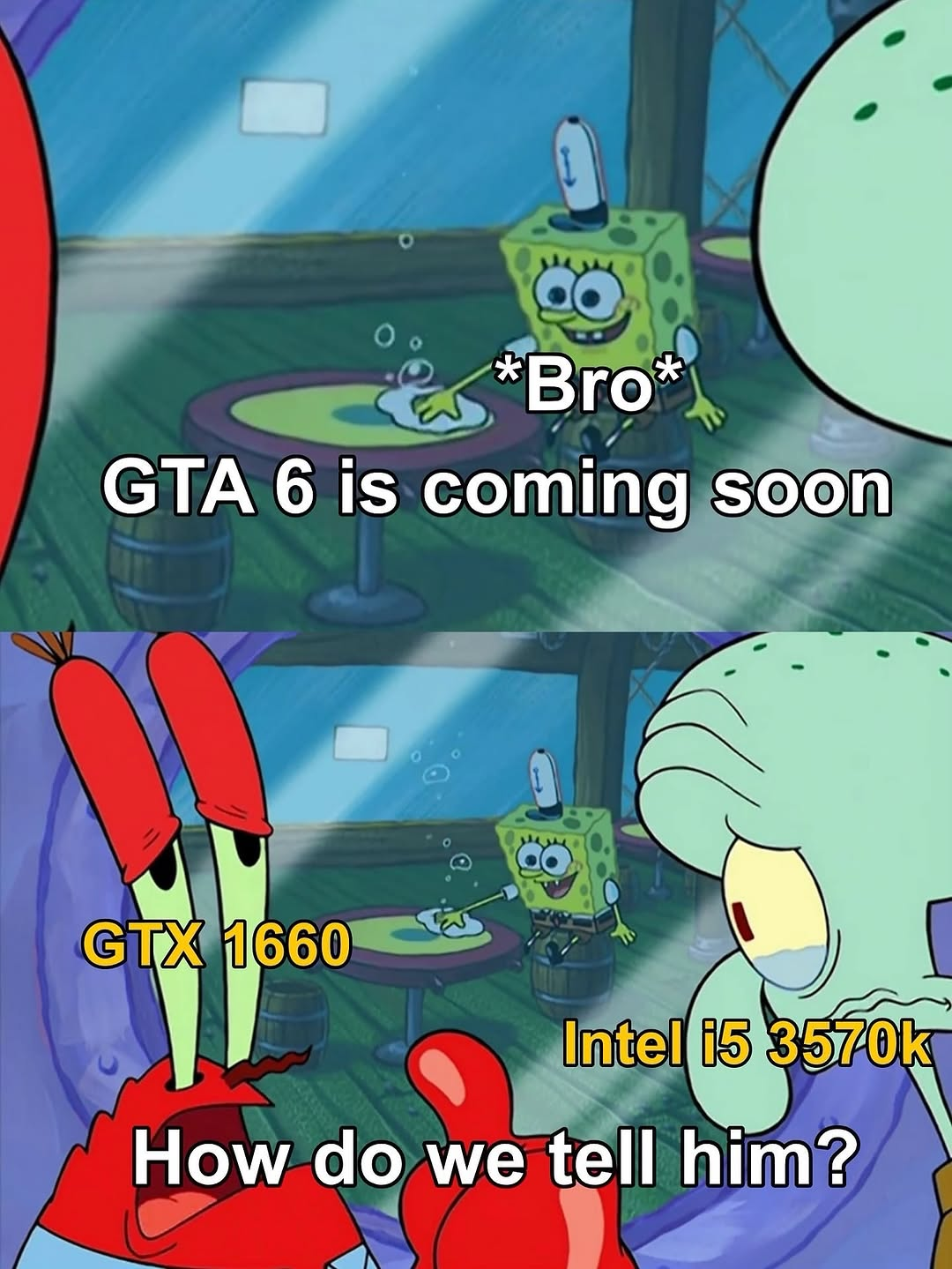
Bro Thinks He'll Play GTA 6… His PC: 'Cute.'
Hardware
241.7K views
2 months ago
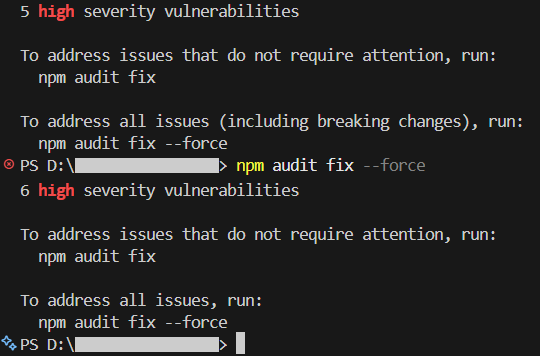
I Know Iknow Ihave To Learn
Programming
169.3K views
1 year ago

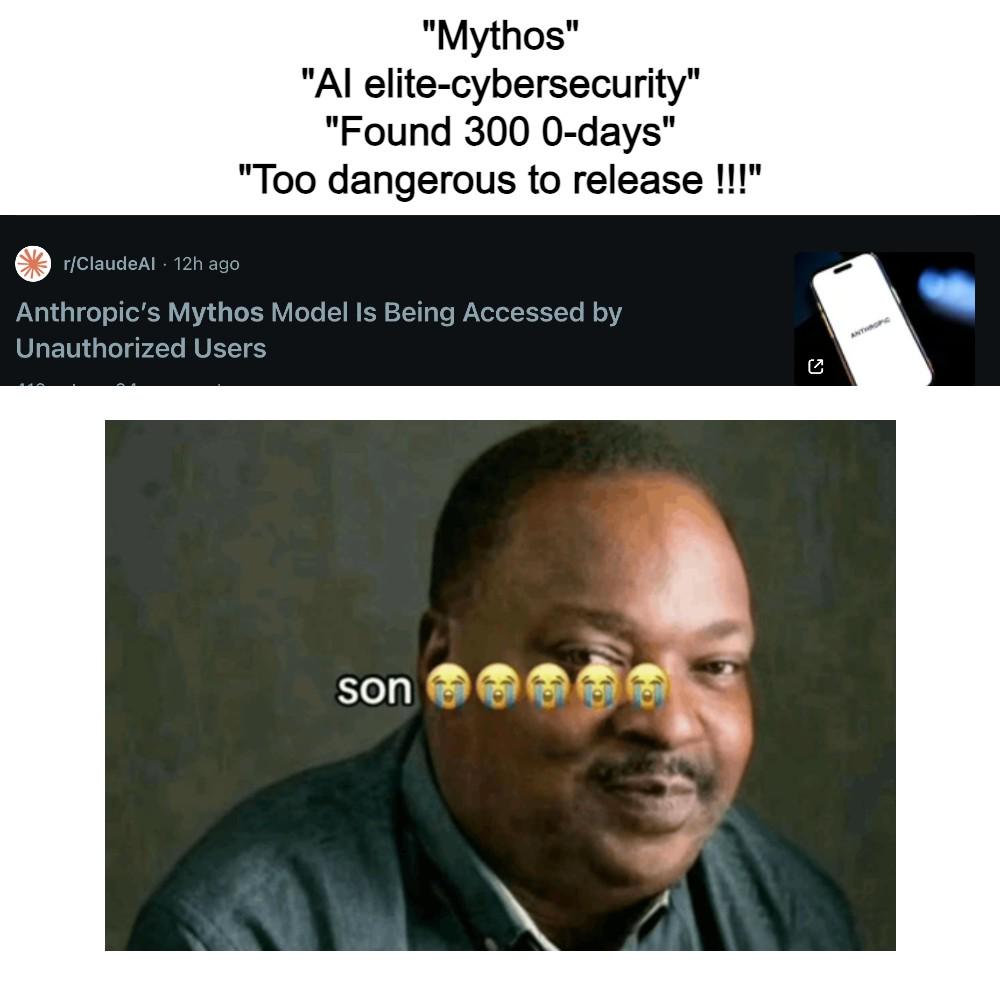
 AI
AI
 AWS
AWS
 Agile
Agile
 Algorithms
Algorithms
 Android
Android
 Apple
Apple
 Bash
Bash
 C++
C++
 Csharp
Csharp