Today's picks
Hacker Poster Binary Code Computer Cybersecurity Posters Decor Matrix Technology Coding Cool Wall Art Print Poster 24x36
Affiliate
$21.99
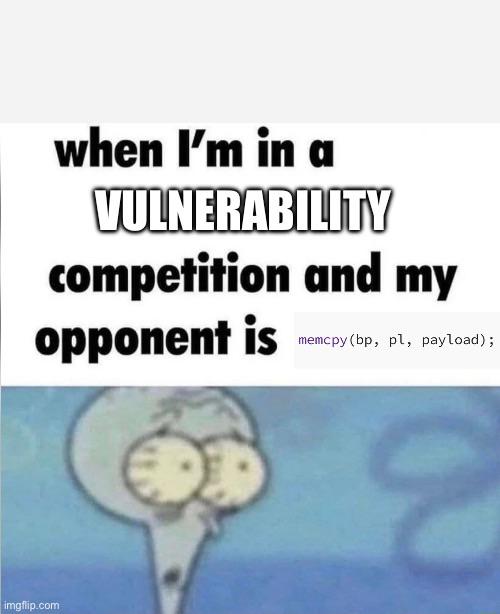
How People Write Comments In Code
Programming
238.9K views
9 months ago
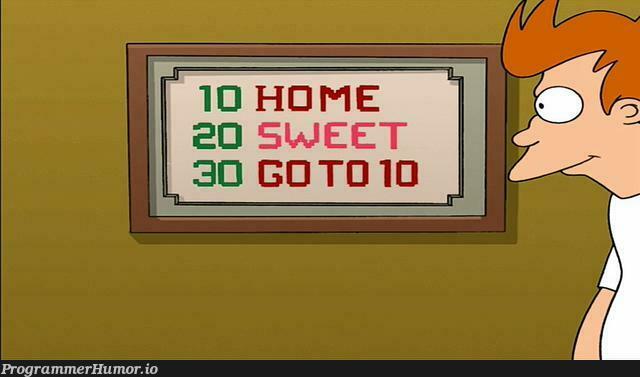
I know just enough BASIC to understand this joke in Futurama
Programming
71.1K views
3 years ago

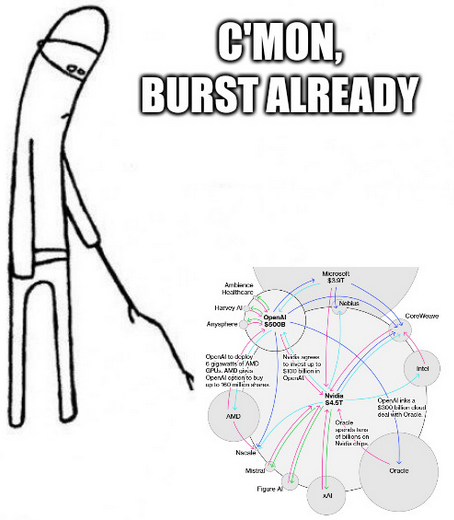
 AI
AI
 AWS
AWS
 Agile
Agile
 Algorithms
Algorithms
 Android
Android
 Apple
Apple
 Bash
Bash
 C++
C++
 Csharp
Csharp