Today's picks

Funny Developer Gifts from Friends - 'Officially The World's Coolest Developer' Black Coffee Mug for Birthday, Unique Gifts for Men, Women, Coworkers, Family
Affiliate
$24.95
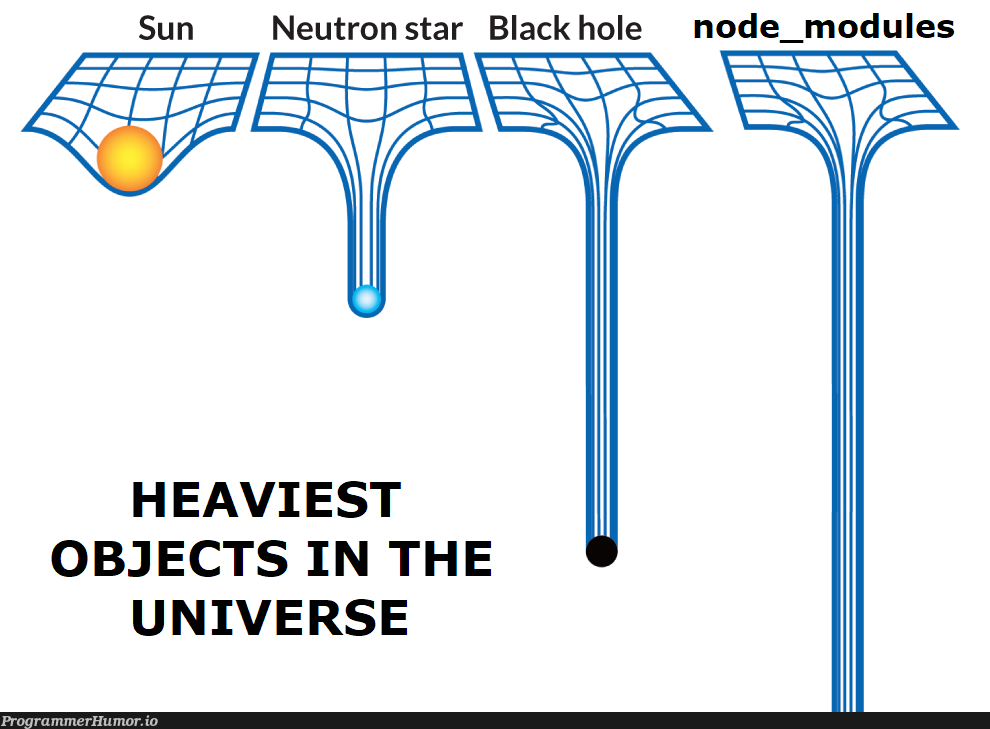
Heaviest Objects In The Universe
Javascript
111.2K views
3 years ago
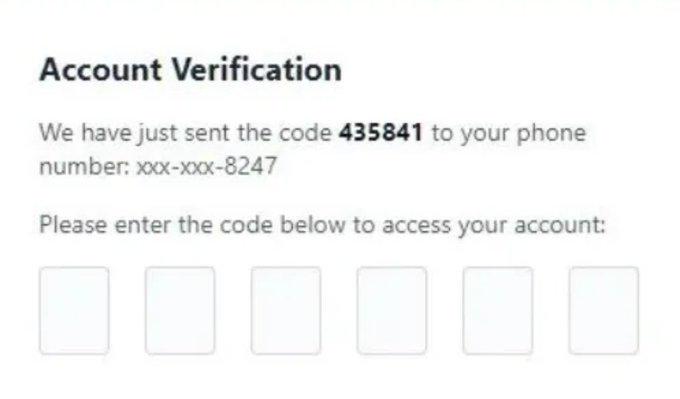
Memorialized For All Time
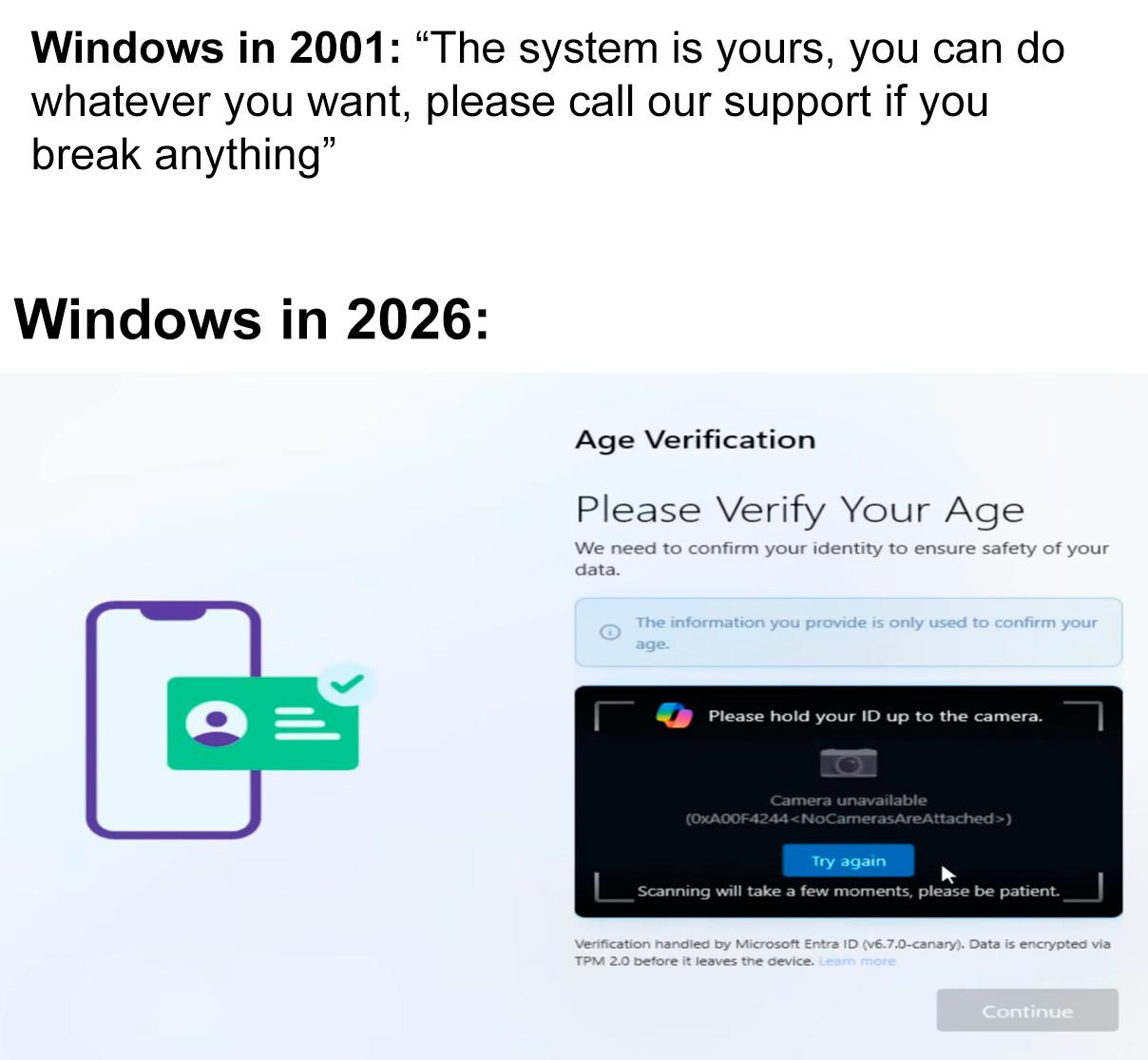
Microsoft
359.2K views
1 month ago

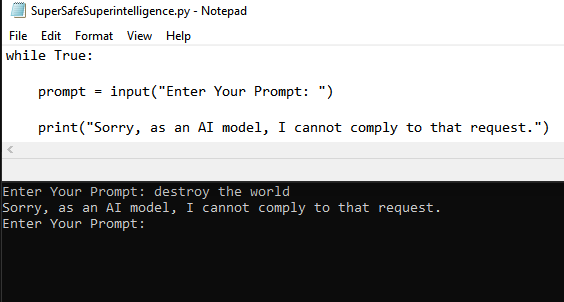
 AI
AI
 AWS
AWS
 Agile
Agile
 Algorithms
Algorithms
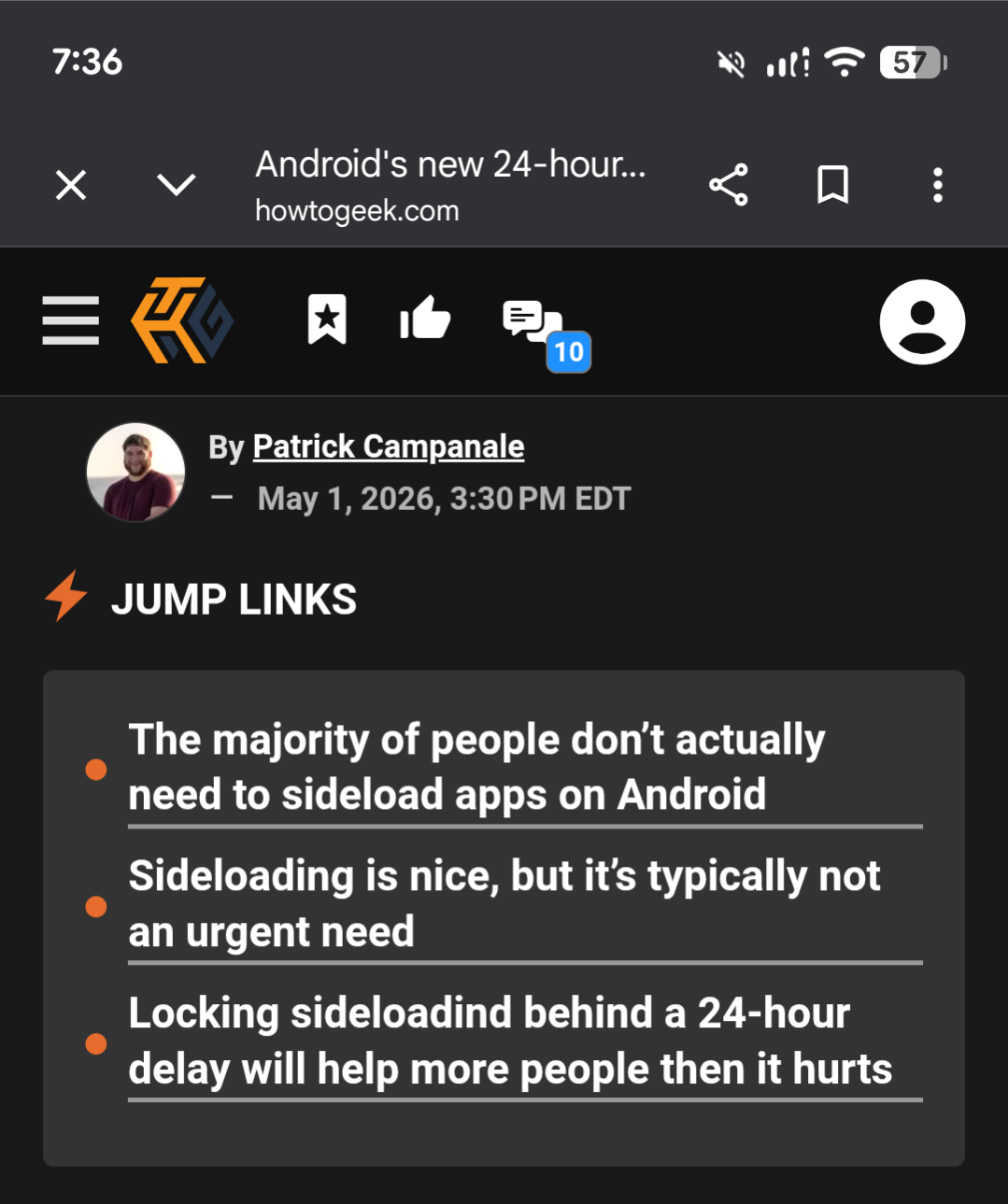
 Android
Android
 Apple
Apple
 Bash
Bash
 C++
C++