Today's picks

Apple 2026 MacBook Pro Laptop with Apple M5 Max chip with 18-core CPU and 32-core GPU: Built for AI, 14.2-inch Liquid Retina XDR Display, 36GB Unified Memory, 2TB SSD, Wi-Fi 7; Space Black
Affiliate
$3349.00

GearScouts.com
Sponsored
Power stations
Suggestion: Internet needs a new filter.
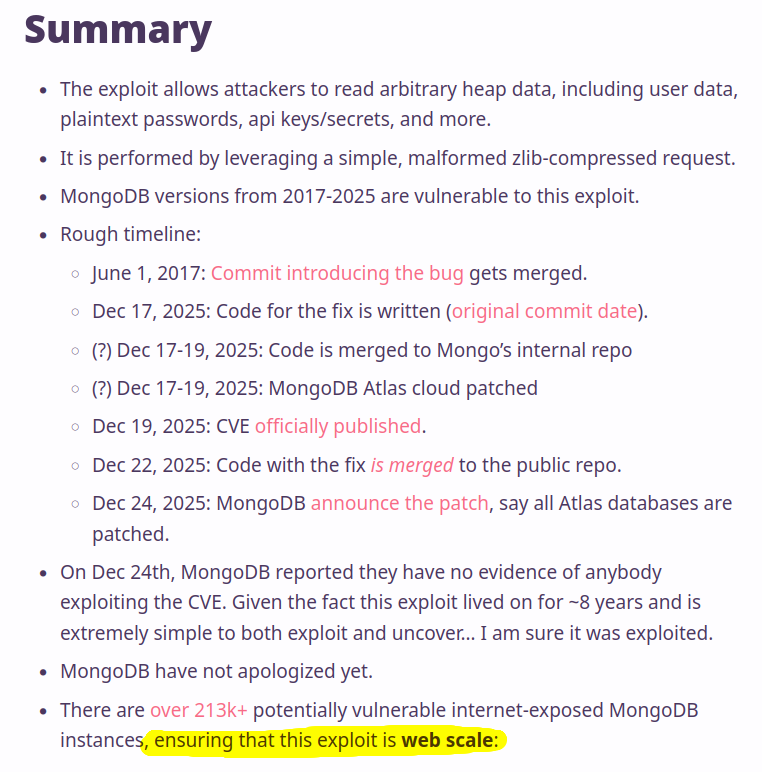
Programming
69.3K views
4 years ago

 AI
AI
 AWS
AWS
 Agile
Agile
 Algorithms
Algorithms
 Android
Android
 Apple
Apple
 Bash
Bash
 C++
C++
 Csharp
Csharp