HTTP 418: I'm a teapot
The server identifies as a teapot now and is on a tea break, brb
HTTP 418: I'm a teapot
The server identifies as a teapot now and is on a tea break, brb
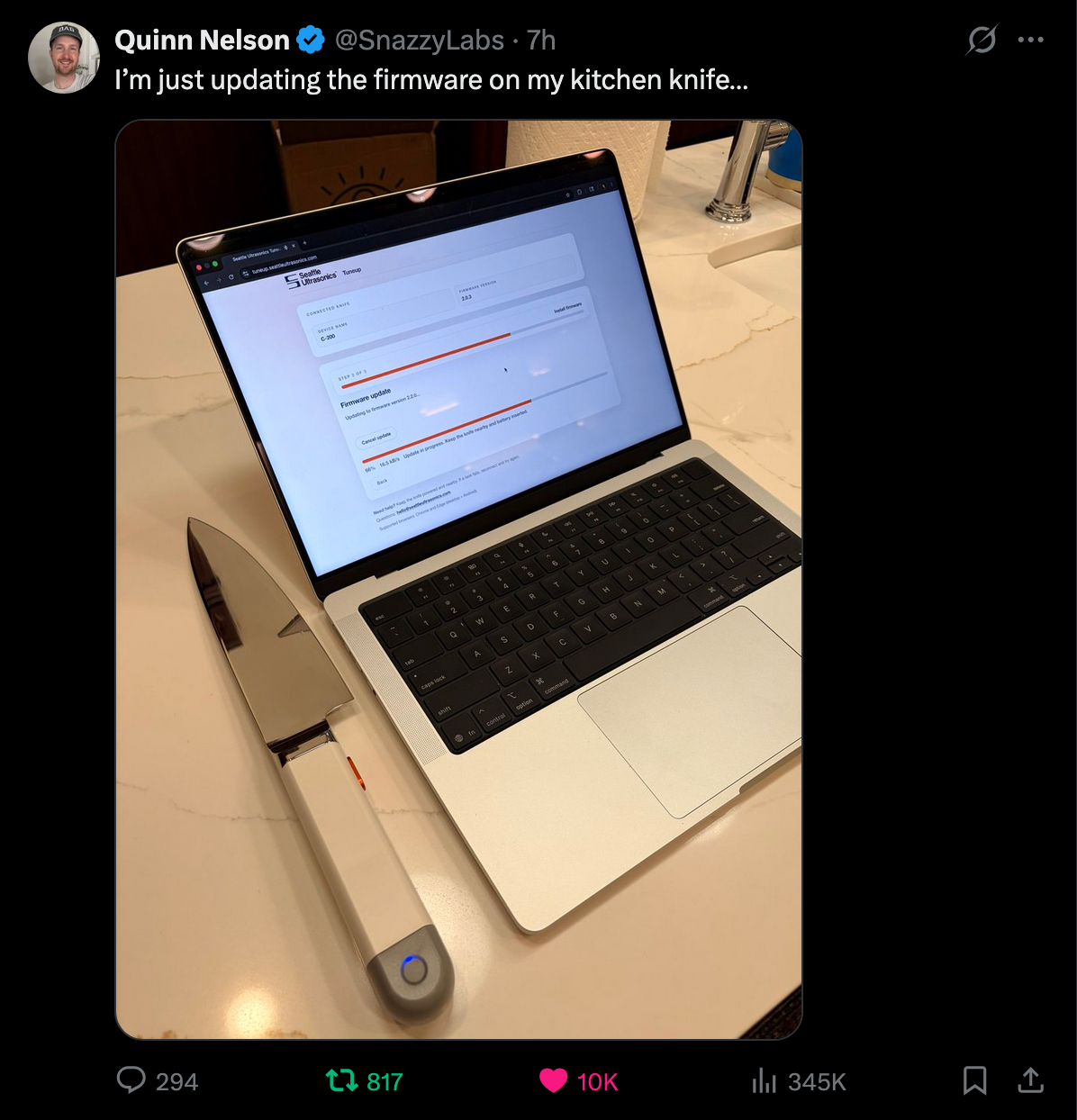
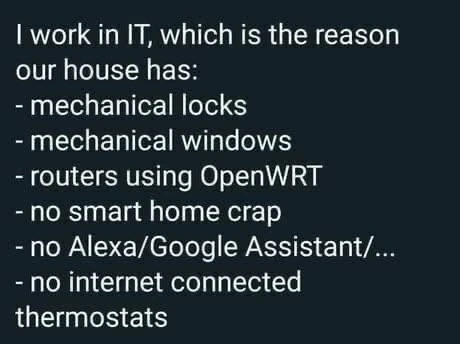
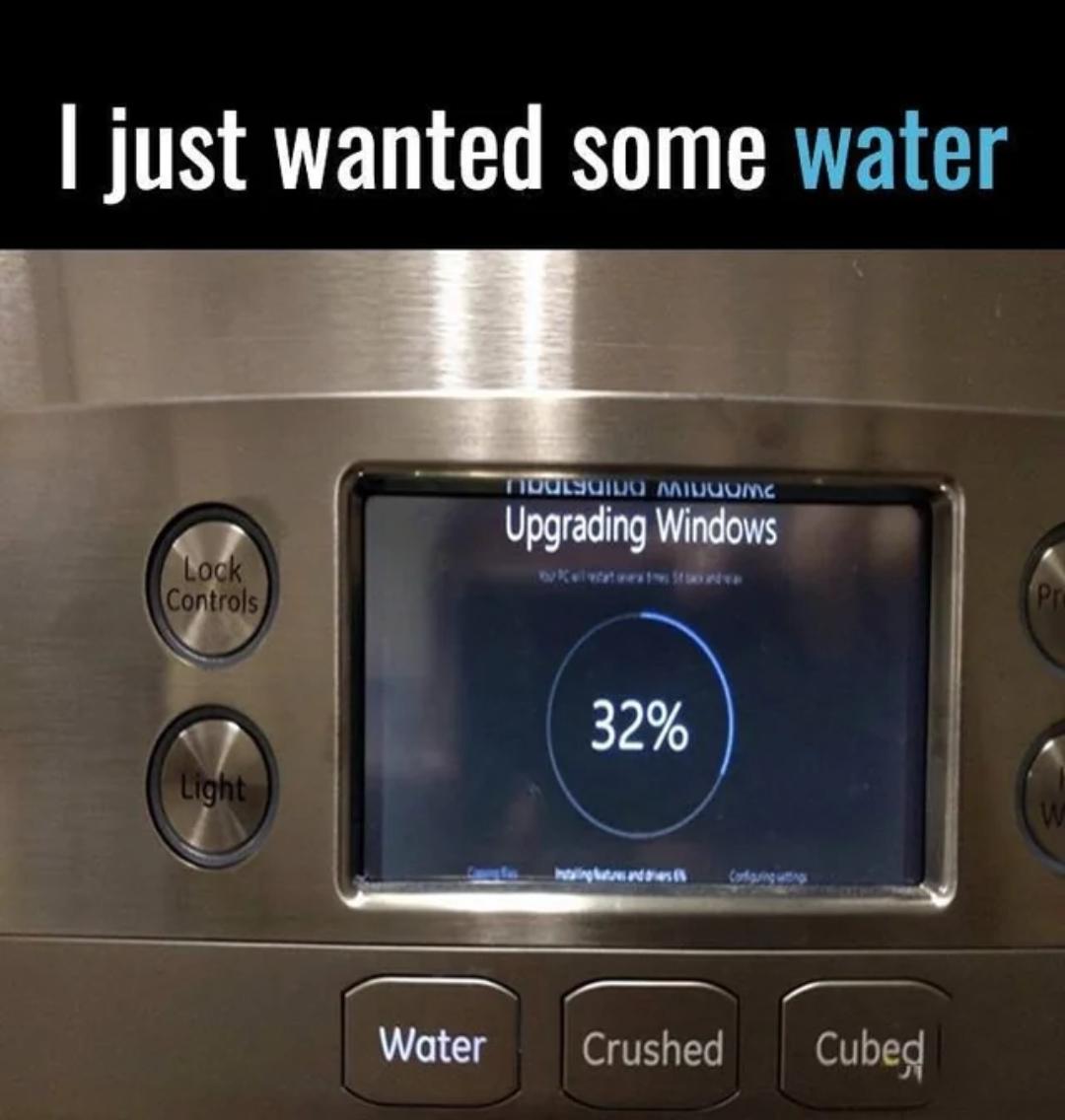
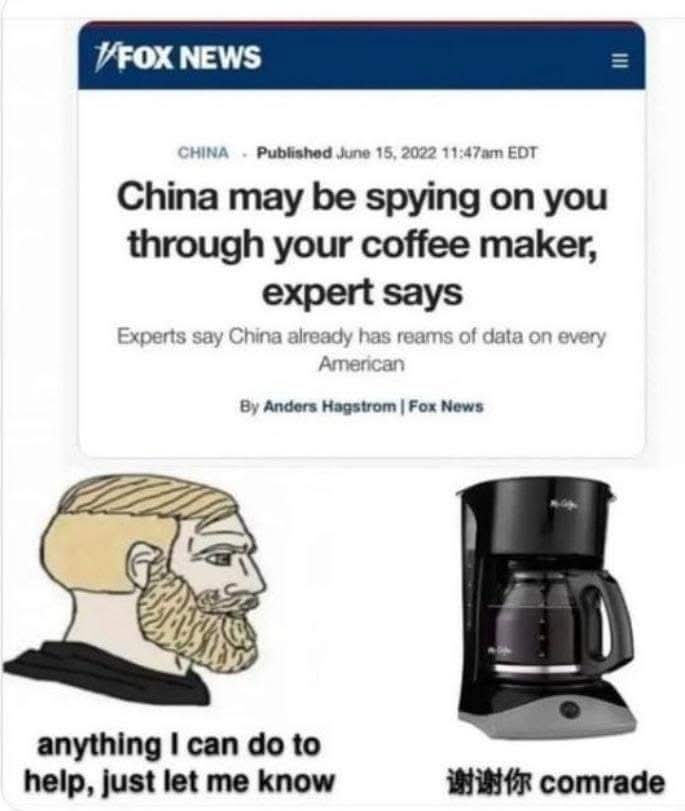
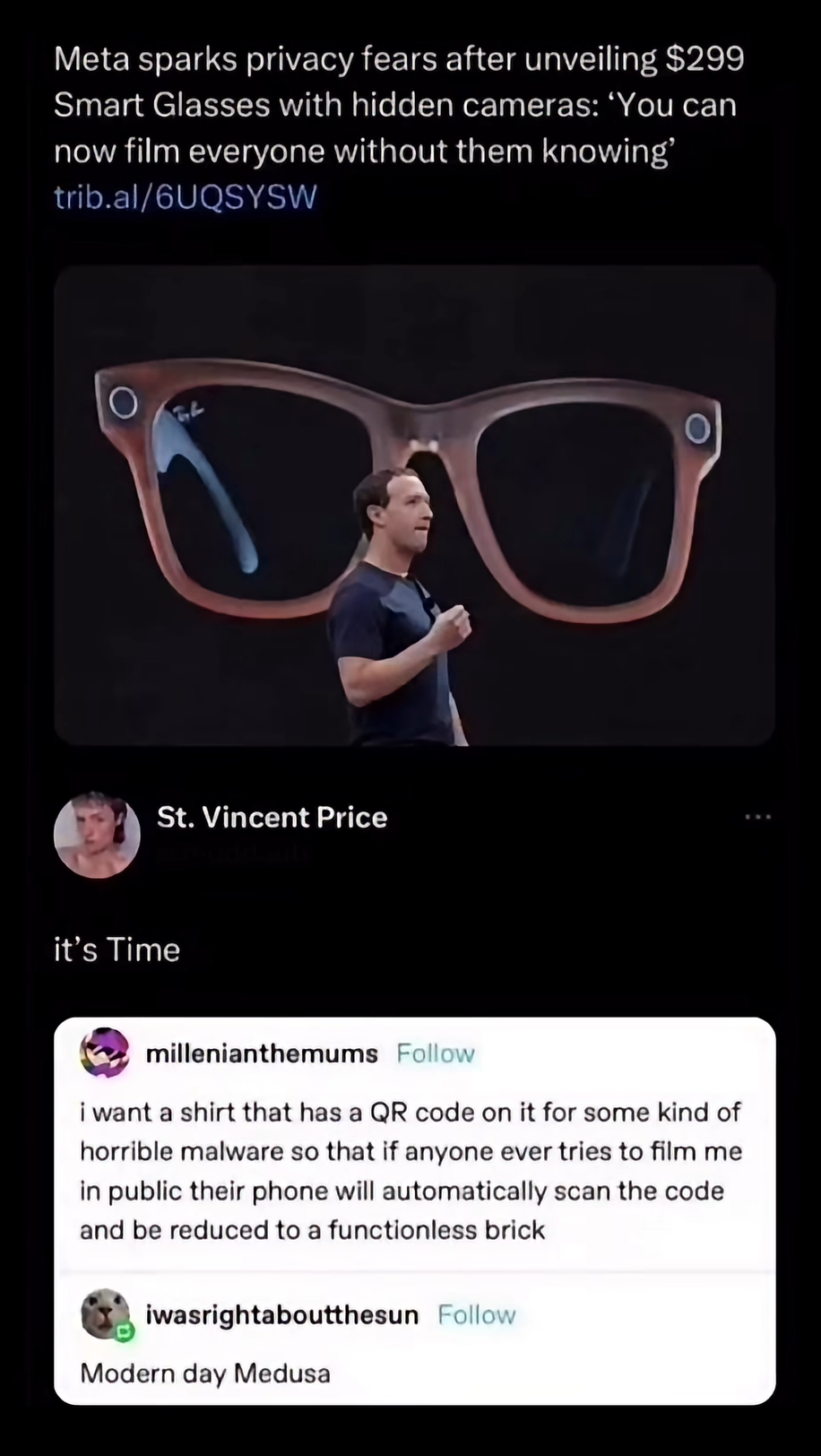
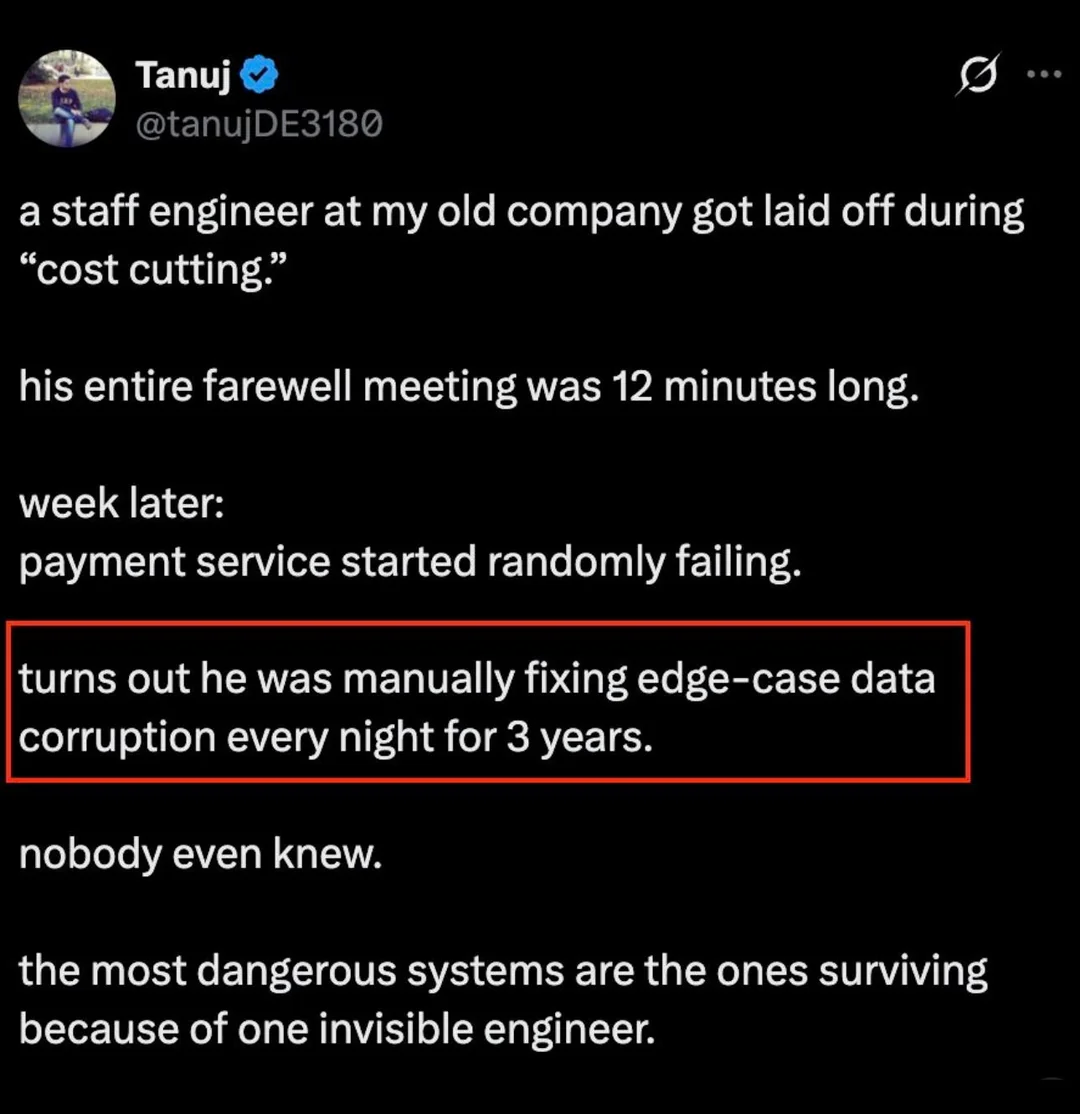
Iot Memes
Internet of Things (IoT): connecting devices that nobody asked to be connected since 2008. These memes celebrate the wild world of smart toasters, refrigerators that tweet, and security cameras with password defaults of "admin/admin". If you've ever wondered why your lightbulb needs a firmware update, struggled to explain to your parents why their thermostat needs WiFi, or created a Raspberry Pi solution for a problem that didn't exist, these memes capture the beautiful absurdity of putting chips in everything and hoping for the best.

 AI
AI
 AWS
AWS
 Agile
Agile
 Algorithms
Algorithms
 Android
Android
 Apple
Apple
 Bash
Bash
 C++
C++