Today's picks

Apple 2025 MacBook Pro Laptop with Apple M5 chip with 10‑core CPU and 10‑core GPU: Built for AI, 14.2-inch Liquid Retina XDR Display, 16GB Unified Memory, 1TB SSD Storage; Space Black
Affiliate
$1499.00
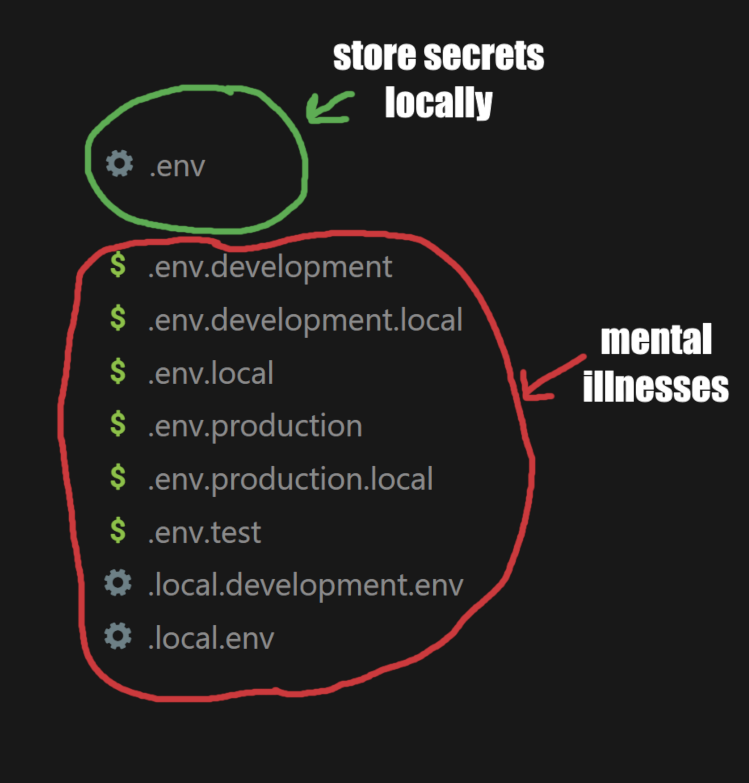
isEven returns if a value is even
Programming
72.5K views
4 years ago
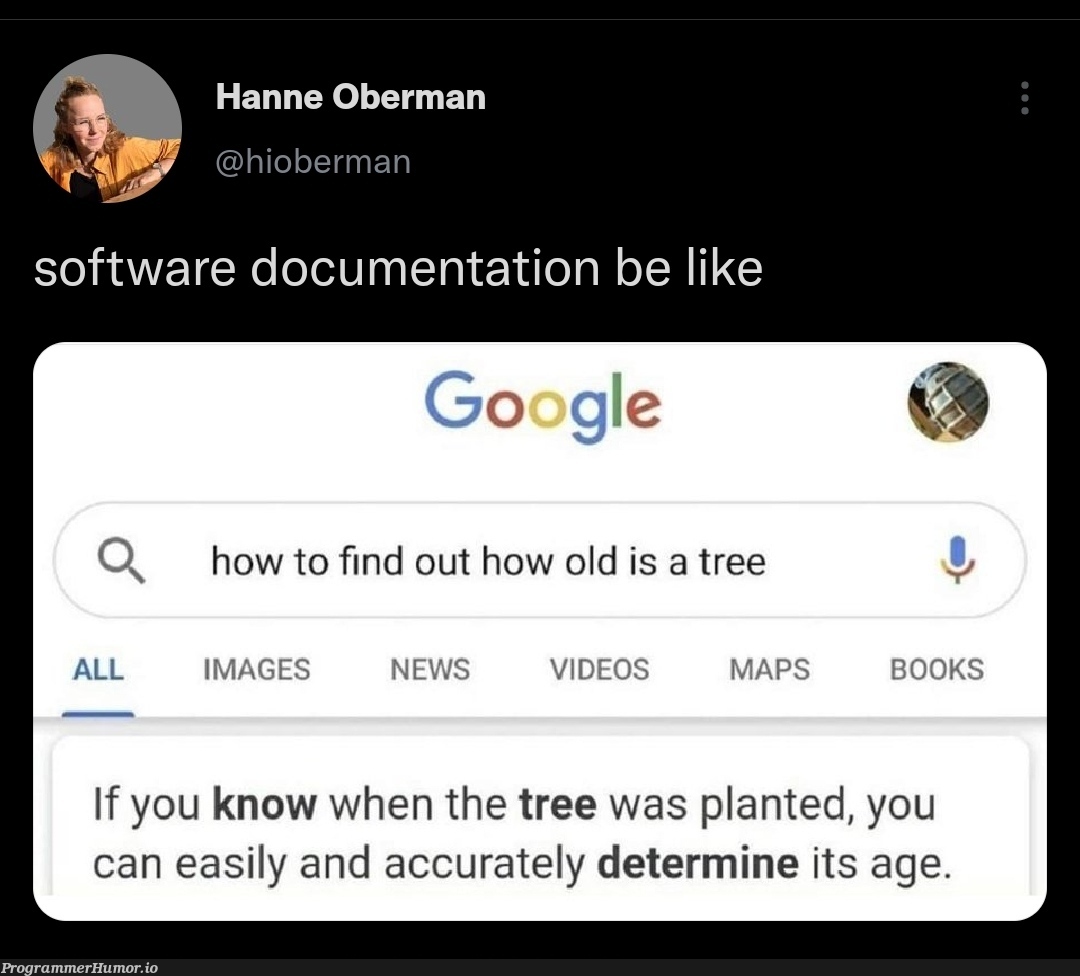
I Will Never Live Up To Their Standards
Databases
66.2K views
2 years ago

 AI
AI
 AWS
AWS
 Agile
Agile
 Algorithms
Algorithms
 Android
Android
 Apple
Apple
 Bash
Bash
 C++
C++